CIA Triad Automation for Law Firms
Published on:
1 Why the CIA Triad is Important For Law Firms
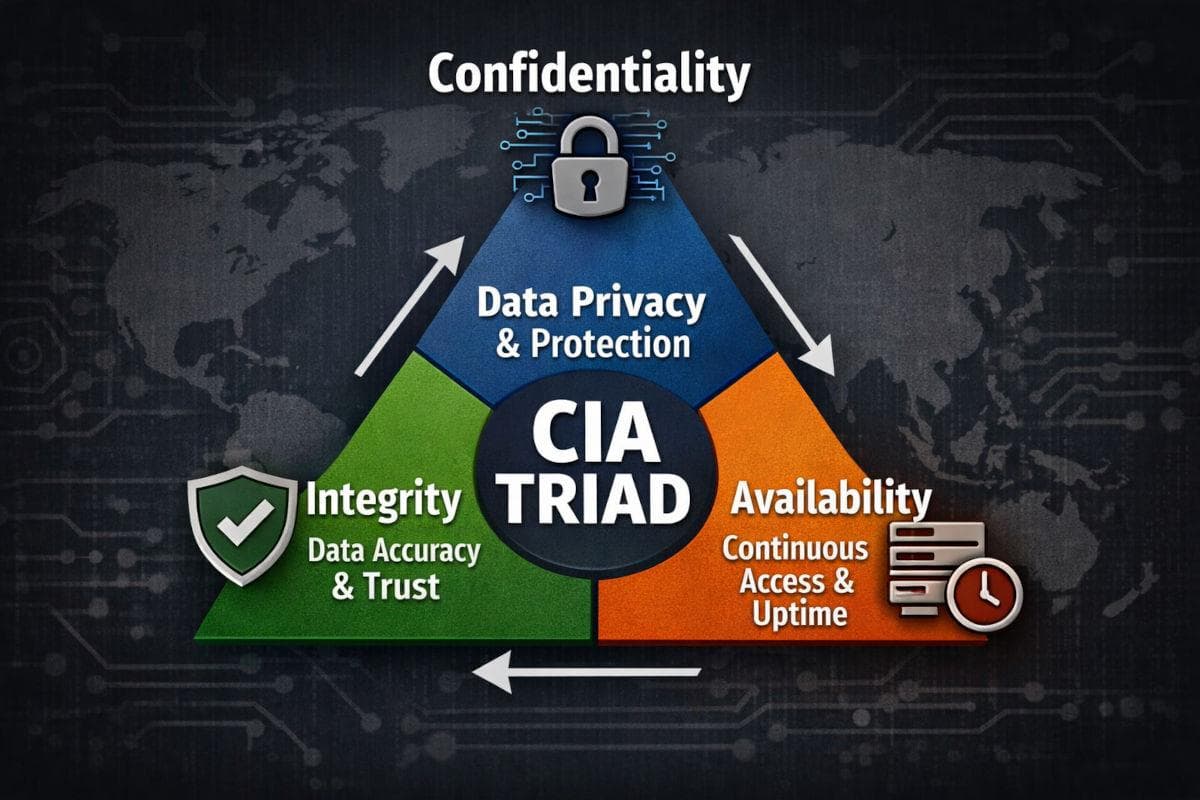
Confidentiality, Integrity and Availability—three words every infosec auditor repeats. For sole practitioners and law firms, the stakes are higher: client privilege, chain-of-custody rules, regulator scrutiny. Yet most legal platforms tackle only one or two pillars and leave the rest to IT. Lexkeep was built to automate all three from the moment a file hits “Upload.”
This article maps each CIA pillar to concrete Lexkeep controls, then shows how it all plays out in real-world legal work.
2 Confidentiality—Keep Eyes Out
How Lexkeep Automates Confidentiality
• AES-256 at rest across EU cloud storage—no toggle, no extra fee.
• Encryption in transit for every connection.
• Optional end-to-end encryption (E2EE): files are cipher-text before they quit the laptop. Lexkeep never sees the key.
• Cohort permissions—Admin, Editor, Viewer—enforced by backend policy, not by “please remember to lock the folder.”
• Single sign-on and MFA for Business & Enterprise tiers.
Impact for Legal Teams
• Privileged docs stay invisible to cloud admins and platform staff.
• A lost laptop or phished password is a nuisance, not a breach.
3 Integrity—Prove Nothing Moved
How Lexkeep Automates Integrity
• File hash (its digital fingerprint) is computed automatically on upload.
• Blockchain anchoring on Ethereum—hash is written to an immutable block with its own timestamp.
• Tamper-evident audit trail—every upload, share, legal hold and deletion request lands in a chained log.
• One-click File Integrity Certificate—uploader, cohort, hash and block number in human-readable PDF.
Impact for Legal Teams
• Produce “proof-of-existence” in hearings without expert testimony.
• Spot silent corruption or accidental edits instantly—hash no longer matches anchor.
• Opposing counsel’s “That’s not the original document” line loses steam in under five minutes.
4 Availability—Be Ready When the Court Calls
How Lexkeep Automates Availability
• Geo-redundant object storage across multiple EU zones.
• WORM-style retention—Write Once, Read Many—prevents silent overwrites.
• Legal-hold switches that freeze evidence for as long as needed.
• Automated soft-delete timers: files disappear from user view, but admins can recover within policy windows (6–12 months).
• 24 × 5 monitoring (Business) or 24 × 7 Sev-1 pager (Enterprise) with tested disaster-recovery run-books.
Impact for Legal Teams
• Ransomware on a local office server no longer halts discovery deadlines.
• “Lost evidence” sanctions become a theoretical risk, not a Friday-night worry.
• Auditors see documented, tested DR plans—one less finding in the report.
5 CIA in Action: A 5-Step Litigation Workflow
1 Upload
Litigation associate drops a deed of assignment into a matter cohort. AES-256 locks it down; Lexkeep hashes and anchors it automatically.
2 Secure Share
Counsel invites an external expert as a Viewer with an E2EE link that expires at a designated time. The expert doesn't need to set up a full account, the audit trail records every access.
3 Legal Hold
When the dispute heats up, the partner flips a legal-hold toggle. No deletes—automatic or manual—will touch that file until the hold lifts.
4 Challenge
Opposing counsel claims the deed was altered after signing. The associate re-hashes the stored PDF. Hash matches the on-chain value anchored 18 months earlier. The claim dies.
5 Exhibit
A File Integrity Certificate goes into the bundle. Judge sees independent timestamp, cohort ID and zero-knowledge blockchain proof. No live witness needed.
6 Feature-to-Standard Mapping (Cheat Sheet)
| CIA Pillar | Lexkeep Control (EXAMPLES) | Typical Standard SATISFIED |
|---|---|---|
| C – Confidentiality | AES-256 encryption at rest · optional E2EE · Cohorts | GDPR 2016/679 Art. 32(1)(a) (2016) ISO/IEC 27001:2022 control 6.6 |
| I – Integrity | Blockchain-anchored hash · WORM storage | U.S. Federal Rules of Evidence 902(13)/(14) (2017 amendments) Nigeria Data Protection Act (NDPA) 2023 s.24(2) |
| A – Availability | Geo-redundant storage · legal hold | ISO/IEC 27001:2022 controls 5.29–5.32 (ICT readiness & capacity for business continuity) ABA Formal Opinion 483 (2018) |
7 What About Cost & Admin?
All the above triggers with a single upload. No extra plug-ins, no on-prem HSM to buy, no blockchain wallet to manage. Starter plans start at €29.99 for solos; larger firms move to Team or Business tiers for SSO and exportable audit logs.
8 Key Take-Aways
• CIA Triad isn’t optional—regulators and judges still measure you by it.
• Lexkeep automates each pillar so fee-earners don’t burn hours on IT tasks.
• Blockchain anchoring delivers courtroom-ready integrity proof with zero crypto jargon for end-users.
• Geo-redundant, WORM-style storage plus legal hold keeps evidence both safe and available.
Ready to see CIA automation in 10 minutes? Book a Lexkeep demo or start a 14-day trial—your next evidence upload will be CIA-compliant before the progress bar hits 100 %.
