End‑to‑End Encryption (E2EE)
Published on: (Updated on: )
Watch End-to-end Encryption (E2EE) video
If you handle sensitive legal or compliance information, you’ve probably heard the term “end‑to‑end encryption.” But what does it actually mean—and why does it matter who controls the keys?
In this article, we’ll explain what E2EE is, why key custody is the real point, and what the future of E2EE may look like as regulators push for more oversight.
1) What End‑to‑End Encryption Is — and What It Isn’t
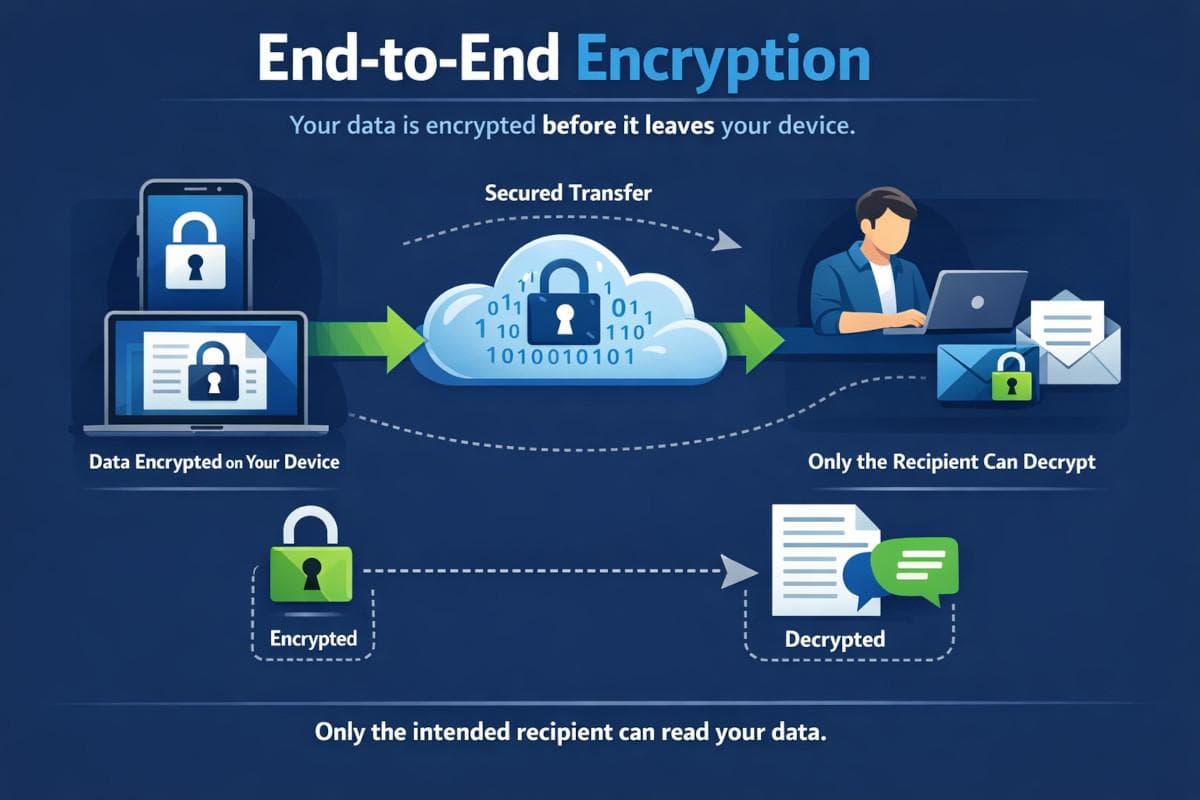
End‑to‑end encryption means your data is encrypted on your device before it leaves, and it can only be decrypted by the intended recipient(s).
So the service provider—whether it’s a messaging app or a file platform—only sees ciphertext, not the readable content.
That’s different from “encryption in transit” or “encryption at rest,” where the provider may still be able to decrypt your data on their servers because they control the keys.
In short:
- Encryption at rest protects stored data from many types of breaches.
- E2EE is designed so the provider cannot read your content at all.
2) Why Key Custody Matters
The most important concept in E2EE is key custody—who controls the encryption keys.
If you control the keys, then:
- the provider can’t decrypt your content, and
- even if the provider is hacked, attackers still can’t read your data without the keys.
Now, a common misconception is that E2EE makes you “immune” to legal requests. The reality is more nuanced:
- If a provider truly does not have your keys, they generally cannot hand over plaintext because they don’t have it.
- But regulators can still compel providers to hand over metadata they do have—like account details, timestamps, IP logs, and who contacted whom.
- And in some cases, authorities may compel the user to disclose keys or decrypted content, depending on local law.
There’s also a trade-off: if you lose your encryption keys or recovery phrase, you may permanently lose access to your data. With true E2EE, there is often no “password reset” that can recover your content.
So E2EE is powerful—but it requires disciplined key management.
3) The Future of End‑to‑End Encryption: Regulation and “Client‑Side Scanning”

Regulators in multiple jurisdictions have expressed concern that E2EE can be abused by bad actors to share illegal content.
As a result, some policy proposals have pushed for ways to detect illegal content without breaking encryption. One approach that has been debated is client‑side scanning—where content is scanned on the user’s device before it is encrypted and sent.
Here’s the key point:
- If a platform scans content before encryption, it can undermine the privacy promise of E2EE, because the device becomes a monitoring point.
To be accurate: not all regulators are demanding this, and not all platforms implement it. But the debate is real, and it’s one reason E2EE is becoming a major policy battleground.
4) Why Purpose‑Built E2EE Tools Matter for Sensitive Legal Work
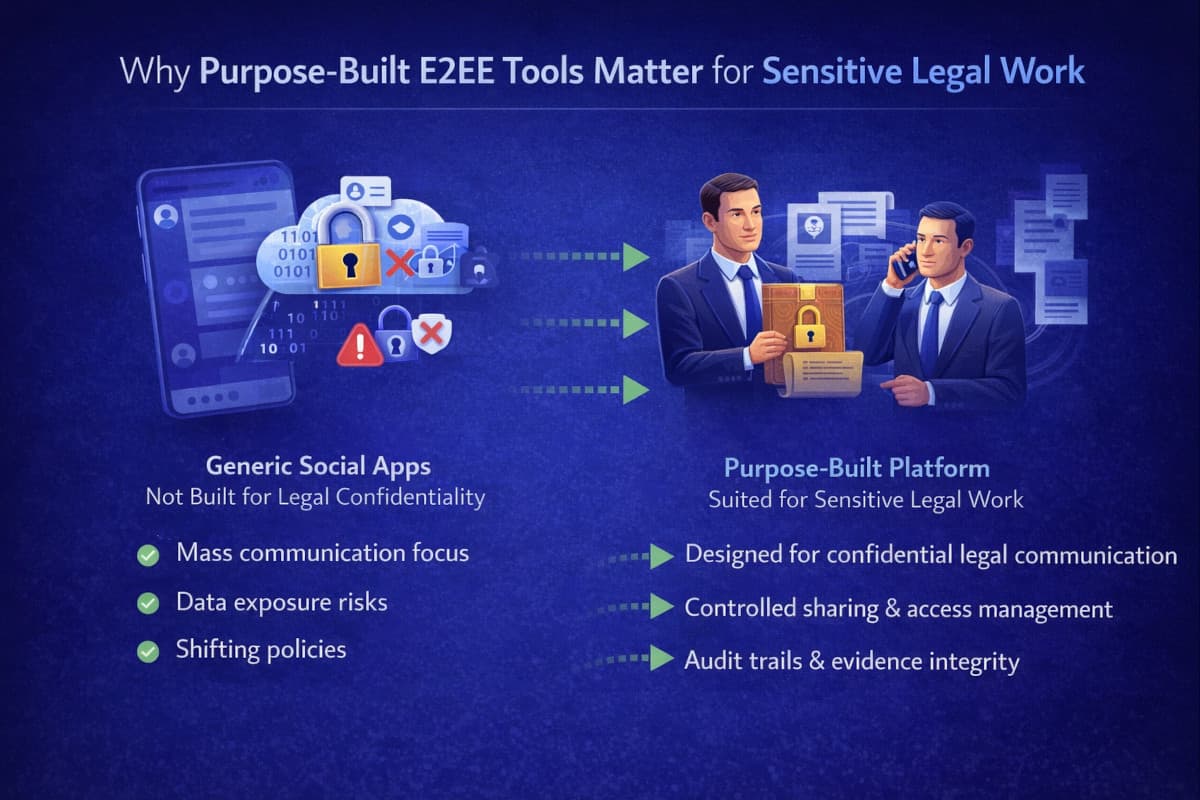
For sensitive matters—like lawyer‑client communications, privileged case files, internal investigations, or regulatory defence—using a purpose‑built tool with E2EE can be safer than relying on generic social apps.
Why?
- Generic apps are designed for mass communication, not legal confidentiality.
- Their settings, backups, and device sync features can create unexpected exposure.
- And their product decisions may change over time due to policy pressure.
A purpose‑built legal platform can offer:
- E2EE designed specifically for confidential legal workflows,
- controlled sharing and access management,
- audit trails and integrity proofs for evidence handling.
5) Where Lexkeep Fits
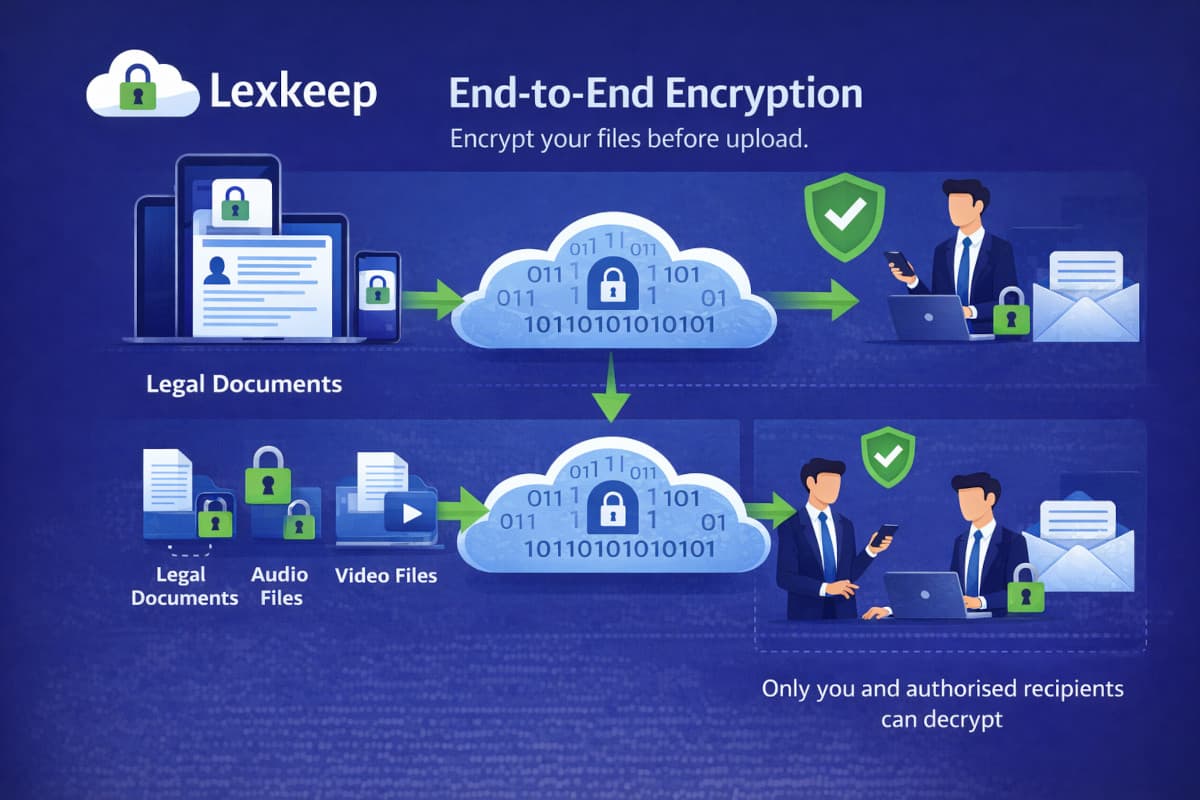
Lexkeep supports encrypted storage for legal documents, audio, and video evidence, and offers optional end‑to‑end encryption so files can be encrypted on your device before upload.
That means:
- only you and authorised recipients can decrypt the content, and
- Lexkeep cannot access plaintext in E2EE mode.
For matters where confidentiality and integrity both matter, Lexkeep also anchors file fingerprints on blockchain to provide tamper‑evident proof of integrity and timing—without putting the file itself on-chain.
End‑to‑end encryption is ultimately about control: who can read your data, and who holds the keys. If you want confidentiality that even the service provider can’t break, E2EE is the gold standard—but it comes with responsibility.
